WebAssembly as an embedding layer for the JVM ecosystem: models, runtimes, and engineering leverage#
Abstract: WebAssembly (Wasm), at the specification level, is not only compact bytecode but an execution model that pins guest modules to host boundaries. When placing Wasm inside the JVM, teams must weigh distribution, observability, and fault isolation between “attached native runtimes” and “pure bytecode hosting”; stacks such as Chicory, QuickJS4J, OPA Wasm, protobuf4j, and Lumis4j show different facets of the same idea—wrapping existing C/Rust/JS assets in versioned artifacts, then exposing them through Java APIs to Spring Gateway, build plugins, or CLIs. The following moves from specification semantics along the dependency chain to benchmarks and sample repositories, and retains verifiable notes on orally cited size figures and slide source paths.
1. Specification lens: modules, host functions, and import/export contracts#
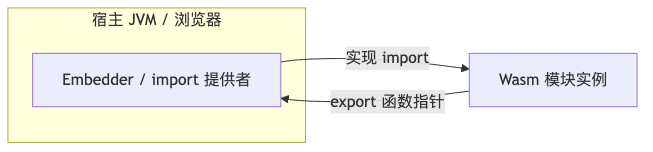
(1) Rationale: Wasm encapsulates computation in typed modules; the host supplies capabilities via import (including host functions implemented by the host), and modules expose callable entry points via export. The same binary can be reused in a browser, a standalone runtime, or an engine embedded in the JVM; differences lie mainly in which imports the host implements. The W3C WebAssembly Core Specification describes Wasm as a low-level code format embeddable in host environments and defines host functions and related concepts separately (WebAssembly Core Specification — overview and semantic model).
(2) Engineering hooks: When reviewing integration, align terminology with instantiation, import, export, invoke, and related terms from the specification; avoid drawing Wasm as an isolated runtime one-to-one with OS processes—instead mark boundaries for “syscall / WASI / custom shim” provided by the embedder.
(3) Usage sketch: A minimal WAT skeleton only expresses “guest calls host logging and exports run”; a real stack still needs memory and tables filled in:
(module
(import "env" "host_log" (func (param i32)))
(func (export "run") (result i32)
i32.const 0
call 0))
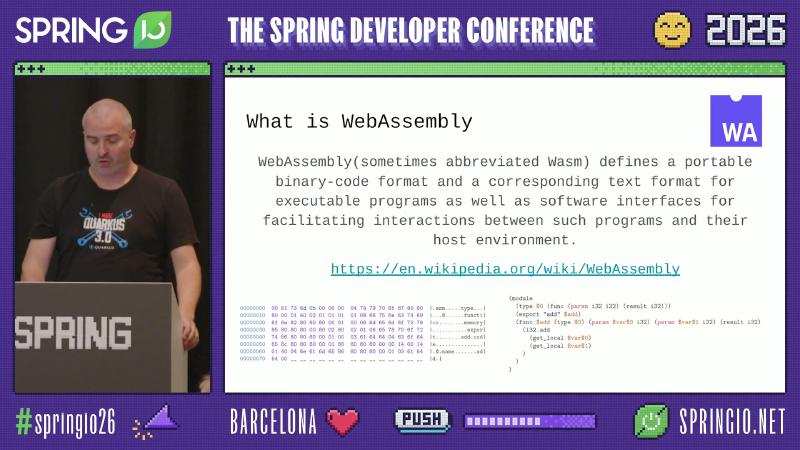
facilitating interactions between such programs and their host environment, consistent with the specification’s emphasis on host interaction; the adjacent WAT fragment illustrates forms such as (param $var$1 i32.
2. Hosting Wasm on the JVM: native FFI paths versus pure Java runtimes#
(1) Rationale: Embedding V8, Wasmtime, or similar native engines via JNI or comparable FFI can preserve peak performance but reintroduces multi-platform .so / .dylib distribution, symbol compatibility, and supply-chain auditing costs; guest-side memory faults also more often surface as process-level failures than controllable Java exceptions. By contrast, a pure JVM bytecode backend pulls execution onto the same observability plane (stack traces, profiler, container image) but may sacrifice some native optimizations.
(2) Engineering hooks: Dylibso Chicory’s documentation and README contrast “attached native + FFI” with “pure JVM” (Chicory README — distribution and runtime positioning). The Foreign Function & Memory API stabilized in JDK 22 (JEP 454) offers an official alternative to hand-written JNI; later approaches such as Redline rely on Panama / jffi-generated bindings.
(3) Usage: A selection checklist can include: whether native artifacts are in the SBOM; whether guest faults map to Error/signal-level behavior; whether tracer and Micrometer metrics lose context across FFI.
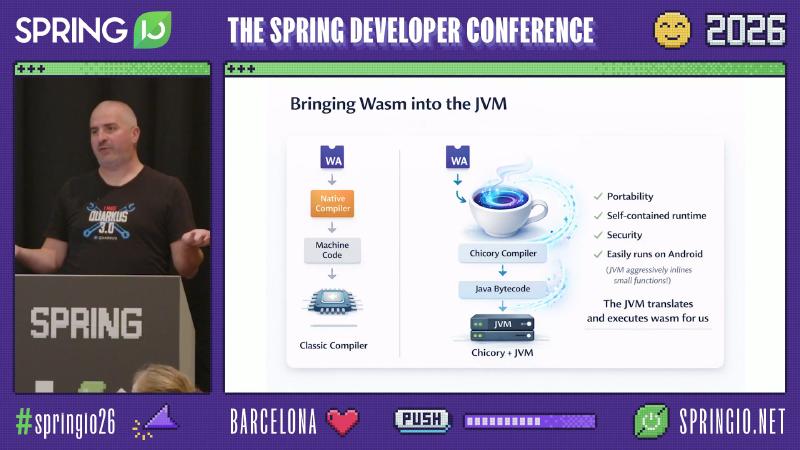
Chicory Compiler, Java Bytecode, Chicory + JVM, and the concluding line The JVM translates and executes wasm for us.
3. QuickJS4J: QuickJS → Wasm → Chicory bytecode → small JAR#
(1) Rationale: Embedding JS on the JVM historically relied on Rhino/Nashorn or larger GraalJS paths; QuickJS4J’s documentation describes a pipeline that compiles QuickJS to Wasm, then uses the Chicory Compiler to produce Java bytecode runnable on any JVM, shipped as a standalone JAR, and states Native-image friendly (QuickJS4J Readme — How it works).
(2) Engineering hooks: Maven coordinates io.roastedroot:quickjs4j; runtime APIs center on Runner and Engine, with host functions bound via @HostFunction / @Builtins (same README Quick Start).
(3) Usage: The official Quick Start recommends:
import io.roastedroot.quickjs4j.core.Runner;
try (var runner = Runner.builder().build()) {
runner.compileAndExec("console.log(\"Hello QuickJs4J!\");");
System.out.println(runner.stdout());
}
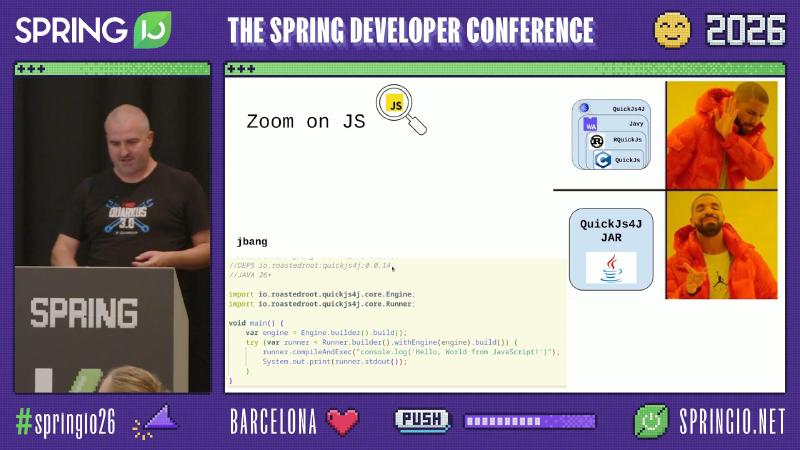
import io.roastedroot.quickjs4j.core.Engine; and QuickJs4J / JAR heading text.
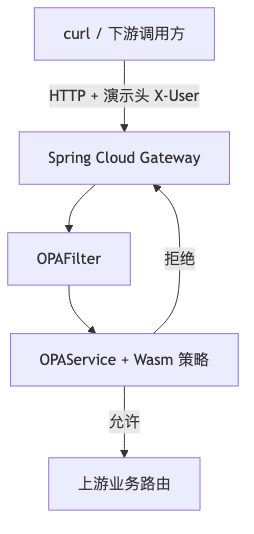
4. OPA: policies compiled to Wasm and evaluated inside Spring Cloud Gateway#
(1) Rationale: The classic topology is business services calling OPA over HTTP; shipping the artifact from Rego opa build -t wasm with the application allows evaluation inside the gateway or microservice process, saving round-trip latency and extra topology (OPA documentation — WebAssembly). On the Wasm path, built-ins such as http.send may not be available and must be implemented by the host (same page).
(2) Engineering hooks: Styra opa-java-wasm provides in-process APIs; examples include OpaPolicy.builder().withPolicy(policyWasm).build() (opa-java-wasm README — Usage). Gateway filters typically extend Spring Cloud Gateway’s AbstractGatewayFilterFactory (exact package and generic signatures per current release); see the official filter factory guide (Spring Cloud Gateway — GatewayFilter factories).
(3) Usage: The X-User header below is a demo convention for passing the subject to the policy layer; on the read side, align with the Rego input schema.
Client probes (printing HTTP status codes):
curl -s -o /dev/null -w "%{http_code}\n" "http://localhost:8081/opa" -H "X-User: Alice"
curl -s -o /dev/null -w "%{http_code}\n" "http://localhost:8081/opa" -H "X-User: Bob"
Receiver-side filter skeleton (illustrative; dependency injection and error mapping omitted; production should avoid long blocking on reactive chains):
@Component
public class OPAFilter extends AbstractGatewayFilterFactory<Object> {
private final OPAService opaService;
public OPAFilter(OPAService opaService) {
this.opaService = opaService;
}
@Override
public GatewayFilter apply(Object config) {
return (exchange, chain) -> {
String user = exchange.getRequest().getHeaders().getFirst("X-User");
if (!opaService.authz(user)) {
exchange.getResponse().setStatusCode(HttpStatus.UNAUTHORIZED);
return exchange.setComplete();
}
return chain.filter(exchange);
};
}
}
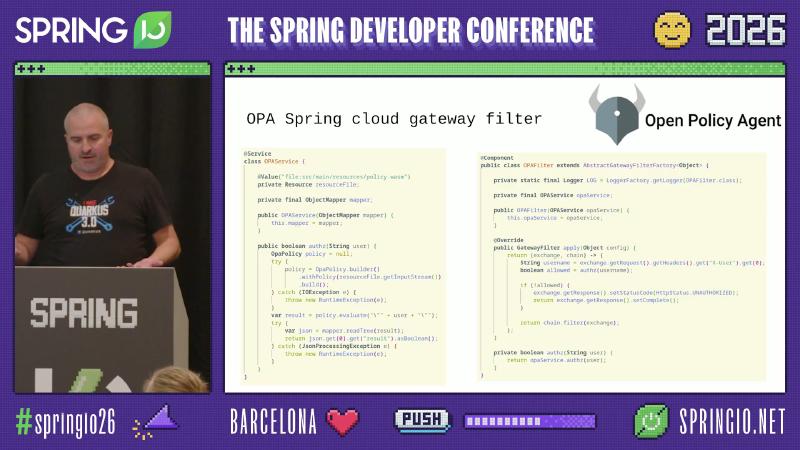
OPA Spring cloud gateway filter Open Policy Agent and public class OPAFilter extends AbstractGatewayFilterFactory<Object.

spring-cloud-gateway-wasm-demos git:(main) and localhost:8081/opa -H"X-User:Alice" (HTTP status in the frame is noisy in OCR; reproduce with a local terminal).
5. protobuf4j: Wasm-izing the protoc toolchain to slim build dependencies#
(1) Rationale: Pulling multi-platform CLIs such as protoc transitively into Java builds can inflate image and cache size; compiling plugins to Wasm and routing through Chicory bytecode replaces the native binary matrix with a single Wasm-artifact approach (motivation from community project narrative and talk track; MB-level comparisons should follow the current repository README and measurements).
(2) Engineering hooks: The protobuf4j README describes “compile protobuf to Wasm → Chicory → pure Java bytecode”, listing protobuf4j-v3 / protobuf4j-v4 and generated plugin mappings (protobuf4j README).
(3) Usage: Normal triggers remain Maven/Gradle builds; plugin coordinates and goals in pom.xml follow repository examples; no fictional groupIds here.
6. Chicory: build-time Wasm→.class and the zero-native dependency story#
(1) Rationale: Chicory’s build-time compiler translates Wasm instructions to JVM bytecode and emits .class files; it positions as a drop-in replacement for the interpreter and shares the same specification tests (Chicory — build-time compilation (docs)).
(2) Engineering hooks: Maven plugin com.dylibso.chicory:chicory-compiler-maven-plugin, goal compile; configuration includes <wasmFile>, <name> (generated class name); the docs also describe interpreterFallback and oversized-function fallback behavior (same page, Interpreter Fall Back).
(3) Usage:
<plugin>
<groupId>com.dylibso.chicory</groupId>
<artifactId>chicory-compiler-maven-plugin</artifactId>
<executions>
<execution>
<goals><goal>compile</goal></goals>
<configuration>
<wasmFile>src/main/resources/guest.wasm</wasmFile>
<name>com.example.wasm.Guest</name>
</configuration>
</execution>
</executions>
</plugin>
7. Capability matrix: alignment cost for proposals, WASI, threads, and more#
(1) Rationale: If the guest enables threads, multi-memory, WASI Preview1, Wasm GC, or similar features, support must match the runtime matrix or a local POC may pass while failing on target JDK/Android.
(2) Engineering hooks: Slides list items such as “Full spec test suite”, “Shared memory + atomics”, “Multi-Memory”, “WASI Preview 1”; authoritative online lists are Chicory README Roadmap and the Wiki comparison (Chicory README — Roadmap · Wiki — WebAssembly feature support).
(3) Usage: Before delivery, run guests’ proposal combinations against the target Chicory version; when mapping WASI to host filesystem/clock/network, verify syscall coverage.

Chicory — Implemented WebAssembly Proposals, with guidance text See the Chicory README and WebAssembly/feature page for details.
8. HotSpot huge methods and the bytecode backend ceiling#
(1) Rationale: Chicory’s documentation states that when Wasm functions grow too large, execution falls back to interpretation and emits guidance bearing the WASM function size exceeds the Java method size limits semantics (Build-time compilation — interpreter fall back). Separately, if HotSpot deems a Java method body over a threshold with relevant flags enabled, it may skip JIT and stay interpreted longer, amplifying the cost of “huge translated units”.
(2) Engineering hooks: OpenJDK sources declare DontCompileHugeMethods and HugeMethodLimit (paths evolve with versions; search the HotSpot tree for your JDK)(OpenJDK — compiler_globals.hpp (mainline snapshot)). Honest caveat: the slide excerpts a jdk11u globals.hpp fragment; whether HugeMethodLimit is a writable -XX: flag in your release must be checked with java -XX:+PrintFlagsFinal; do not assume production tunability by default.
(3) Usage: When seeing Chicory compile warnings or throughput anomalies, cross-check diagnostics such as -XX:+PrintCompilation with Chicory fallback settings.
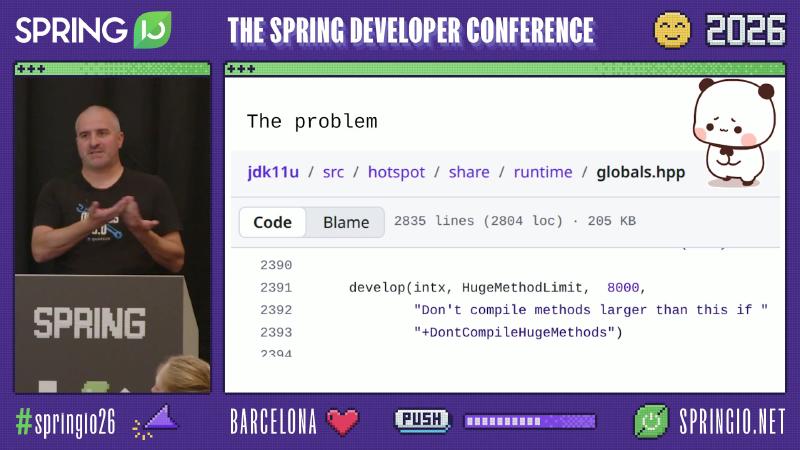
The problem and source line develop(intx, HugeMethodLimit, 8000, and "Don't compile methods larger than this if ".
9. Chicory Redline: Cranelift machine code path, mmap, and Panama/jffi#
(1) Rationale: Redline’s readme contrasts with “Wasmtime + JNI”: build time compiles Cranelift (the same codegen backend as Wasmtime) itself to Wasm, runs it under Chicory to produce machine-code resources; run time **mmap**s executable pages, uses Panama FFM on JDK≥25 and jffi on JDK≥11; unsupported platforms fallback to pure Chicory bytecode (chicory-redline README — How it works · Dylibso post — Chicory Redline).
(2) Engineering hooks: Maven coordinates include io.roastedroot:redline and redline-compiler-maven-plugin; README examples show MyModule.builder().build(), instance.export("my_function").apply(), instance.isNative(), and similar API shapes (per that README).
(3) Usage: Locally verify whether isNative() hits the native backend; CI matrices should cover platforms without native artifacts to exercise fallback.
10. Benchmarks: wasm-score shootout and multi-runtime comparison#
(1) Rationale: The public wasm-score repository’s shootout adapts The Computer Language Benchmarks Game to compare Wasm host implementations (wasm-score — benchmarks/shootout README). Millisecond/second figures in slide tables depend heavily on hardware, JDK, and Chicory/Redline versions; readers should reproduce with a fixed harness rather than quoting a single screenshot.
(2) Engineering hooks: Labels such as chicory-redline, wasmtime, wazero correspond to different hosts or compile backends; names like shootout-ed25519, shootout-heapsort are benchmark names.
(3) Usage: Clone the Bytecode Alliance repository and run benchmark targets per its README; when comparing, record JDK java -version, CPU model, and turbo state.
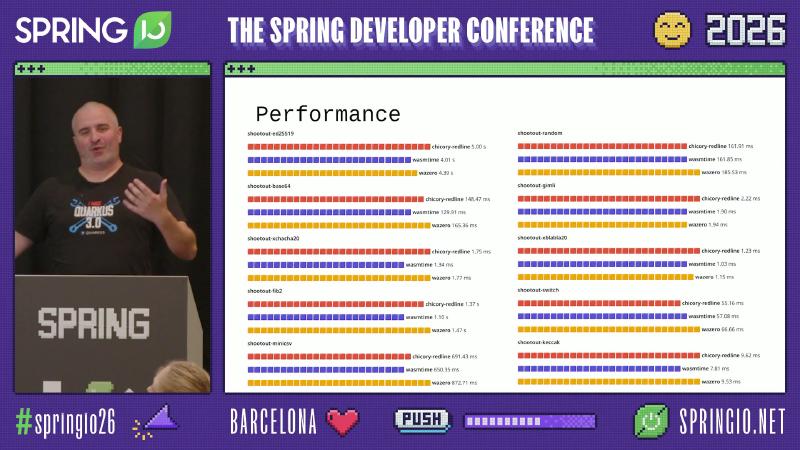
shootout-ed25519 and columns chicory-redline, wasmtime, wazero.
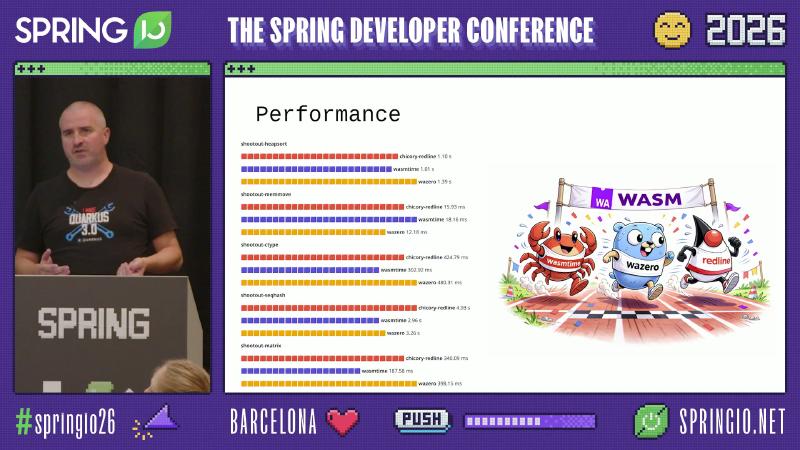
shootout-heapsort, shootout-memmove, chicory-redline 15.93 ms, wasmtime 18.16 ms, and similar.
11. Lumis4j and TamboUI: Wasm motivation for terminal syntax highlighting#
(1) Rationale: The Lumis4j README states it is based on Tree-sitter and runs highlighting logic in pure Java via Wasm through Chicory (lumis4j README). The TamboUI README positions itself as a modern terminal UI library for Java, analogized to Rust ratatui and Go bubbletea (tamboui README); alongside the highlighting stack, the engineering story is “terminal UI wants editor-grade coloring with no first-class JVM story.”
(2) Engineering hooks: Lumis4j offers Lumis.builder(), withLang, withTheme, Formatter.TERMINAL (ANSI), and combinations; official examples also include an HTML inline formatter enum.
(3) Usage:
try (var htmlLumis = Lumis.builder()
.withLang(Lang.JAVA)
.withTheme(theme)
.withFormatter(Formatter.TERMINAL)
.build()) {
// htmlLumis.highlight(...) — concrete calls per README
}

Lumis4j, lumis4j git: (9e4c43a), and code line try (var htmlLumis = Lumis.builder().
Code highlight, README .md, and sentence AJava library for building modern terminal user interfaces. (OCR merged “A Java” into “AJava”; quoting preserves the frame typography.)
12. Runnable sample: spring-cloud-gateway-wasm-demos#
(1) Rationale: A single slide cannot cover how Gateway routes, filter beans, and Wasm artifact loading fit together; the public demo repository gathers multiple Wasm-style filter demos in one place, default mvn spring-boot:run, port 8081 (spring-cloud-gateway-wasm-demos README).
(2) Engineering hooks: The repository extends wasm-gateway-filters and notes switching to Chicory; concrete module layout follows pom.xml.
(3) Usage: Clone and start modules per the README; align host and path in the earlier curl examples with sample routes.
References and further reading#
- WebAssembly Core Specification — semantics, host, and module model
- Chicory README — pure JVM versus native embedding
- Chicory — build-time compilation and interpreter fallback (docs)
- Chicory Wiki — WebAssembly feature matrix
- JEP 454 — Foreign Function & Memory API (JDK 22)
- OpenJDK HotSpot — JIT-threshold declarations in
compiler_globals.hpp(mainline snapshot) - QuickJS4J Readme — pipeline and Quick Start
- OPA documentation — WebAssembly builds and constraints
- Styra opa-java-wasm — in-process evaluation examples
- Spring Cloud Gateway — GatewayFilter factory reference
- protobuf4j Readme — Wasm-ized protoc plugins
- chicory-redline README — Cranelift, Panama, jffi, and fallback
- Dylibso — Chicory Redline introductory post (Markdown in repo)
- wasm-score — shootout benchmark notes
- lumis4j README — Tree-sitter + Chicory highlighting stack
- tamboui README — terminal UI positioning
- spring-cloud-gateway-wasm-demos — Gateway + Wasm demo collection



